US official says, No one can repel another WannaCry attack
US official says,No one can repel another WannaCry attack
US official says, No one can repel another WannaCry attack :
A senior cybersecurity official said the US government may not be able to prevent further global cyberattacks, similar to the WannaCry attack in 2017.
Janet Manfra, assistant director of cybersecurity for the US Department of Homeland Security’s Cybersecurity and Infrastructure Security Agency, said on stage at the TechCrunch Disrupt SF conference that the WannaCry attack, which infected hundreds of thousands of computers worldwide, Video grab – it was a unique challenge to its ability to spread quickly. He added: “We have seen something that shows itself exactly as a worm. I think the original perpetrators probably did not expect this effect. ”
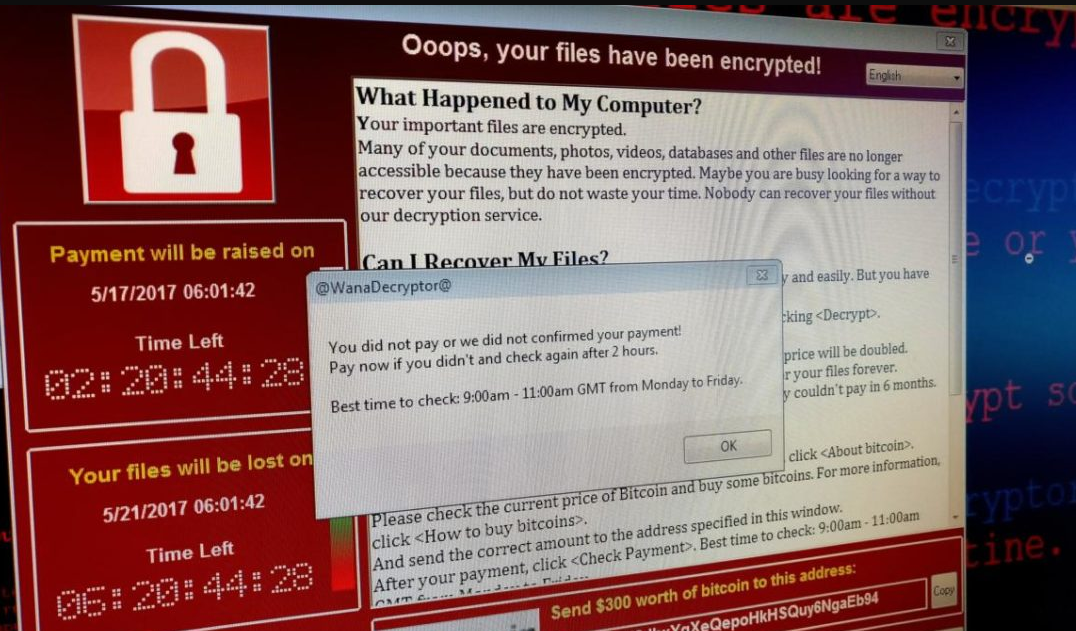
The WannaCry attack was the first major global security incident in years, in which hackers – believed to be linked to North Korea – using a series of dangerous hacking tools stolen just weeks before the US National Security Agency, which was posted online.
These tools allowed anyone using them to infect thousands of vulnerable computers with a back door. That back door was used to deploy Wanna Cry software, which prevented users from opening their devices and accessing their files unless they paid a ransom.
Related Posts
To make matters worse, Wana Cry’s ability to rapidly deploy, allowing it to infect entire devices in a single network, then harder to contain. Although the NSA did not publicly acknowledge the theft of its hacking tools, the Department of Homeland Security said at the time that the users were the first line of defense against the WannaCry threat. Microsoft launched security updates weeks before the attack, but many devices have not yet installed them.
“Installing security updates can prevent a good number of people from becoming victims,” Manfra said. But two years after the attacks, the data shows that more than a million computers are still vulnerable to malware ransomware.
“Bad things are coming,” Manfra said, but those efforts to mobilize the government and private sectors could help fight cyberattacks as they emerge. She added: “Fortunately, there was someone who was able to find a way to eliminate them, and did not affect the United States much.”
The British engineer and security researcher (Marcus Hutchins) had registered a domain name found in the source code of the malware, and by recording that name was able to eliminate the software and prevent its spread.
Hutchins gained worldwide fame overnight in the ethical hacker community in May 2017 for his role in overcoming the WannaCry attack, which infected hundreds of thousands of computers and caused disruptions in factories, hospitals, shops, and schools. More than 150 countries.
Manfra’s comments come a few weeks after her administration warned of a new emerging threat posed by BlueKeep, a vulnerability in Windows 7 and earlier, and experts say it has the ability to launch another global attack similar to WannaCry. ). BlueKeep can be exploited to run malicious code – such as malware or ransomware – on affected systems.
Like Wanna Cry, BlueKeep has the ability to rapidly deploy, allowing it to infect entire devices in a single network, and then difficult to contain. It is estimated that more than one million devices are vulnerable to this malware. Security researchers say it is only a matter of time before abusive actors develop and exploit the loophole to carry out a global cyberattack.

